Hi there,
I’ve already got my new FOB keys PicoPass 2k. I tried everything in the post referenced, but it doesn’t work.
I’m trying to understand everything. So I guess this FOB Key has more security than I expected.
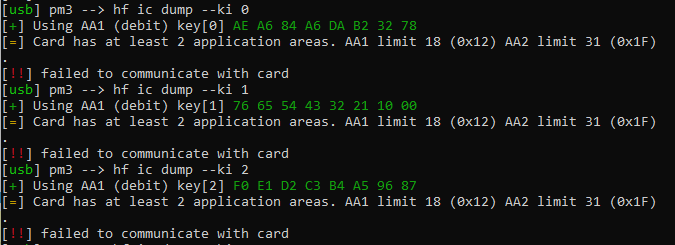
hf ic dump --ki 0
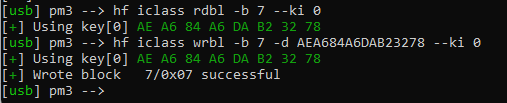
hf iclass rdbl -b 7 --ki 0
hf iclass wrbl -b 7 -d AEA684A6DAB23278 --ki 0
It doesn’t work ![]()
Also, I read your article @AustralianElectrical on https://forum.dangerousthings.com/t/need-help-cloning-hid-iclass-legacy/16334/6 I don’t have access to the reader.
Any other Ideas?