Yeah so the problem is that TagWriter has a bug with password retention.
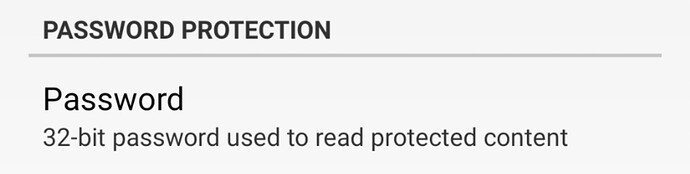
First set the tag up for read protection.
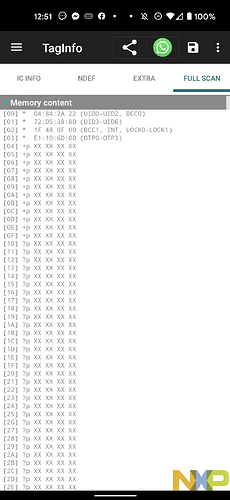
Can’t read with TagInfo. Success.
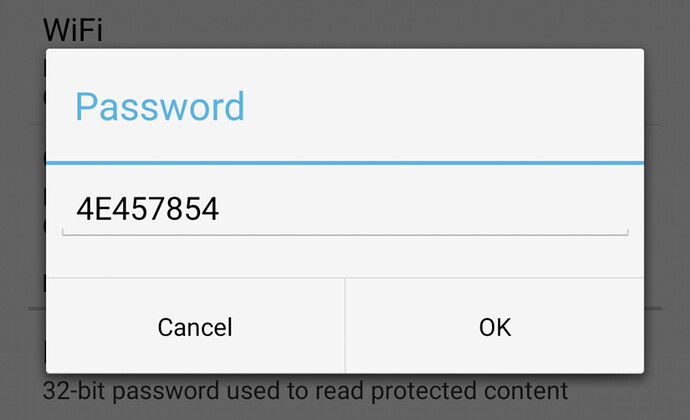
Go to TagWriter preferences, set the password.
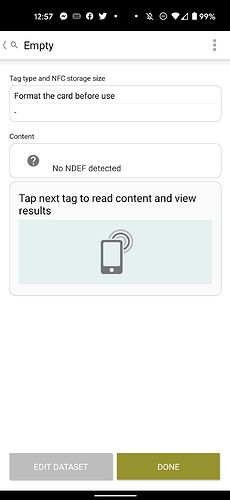
Exit preferences screen and try to read tag data… days empty which is not true. There is a URL record written in there.
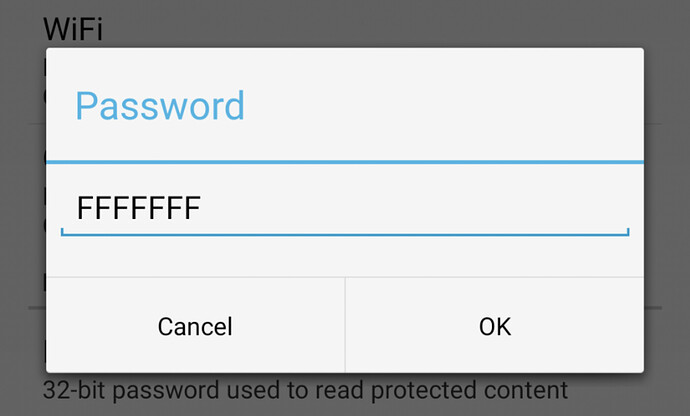
Go back to preferences and see the password is default FF FF FF FF.
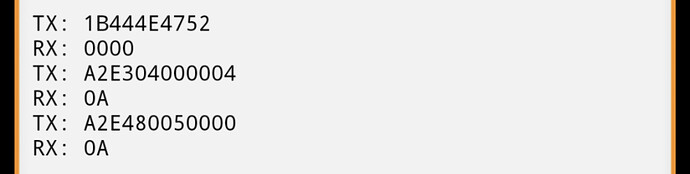
I think the default display of the factory default password (FF FF FF FF) is actually a security setting… meaning you can’t get someone’s password by going there and looking… but… I also don’t think it’s actually saving the user entered password, or passing it the password to the chip either… pulling out Proxmark3 to sniff traffic…