Awesome, I’ll sort that out when I’m back on a PC.
Thanks
I’m still here, just lurking ![]() Feel free time edit as appropriate but please make a transparent edit.
Feel free time edit as appropriate but please make a transparent edit.
As long as identity is ok with it, I’m good. I was just looking to leave a comment if anyone got stuck and that seemed to fix it.
@identity Looking at your hand, it looks like the needle came from the opposite angle that’s described in the instructions that I’ve found. Just curious what the reason/story was behind that
Injecting the chip in this was is actually better in most repects as if you slip of “go too deep” the needle is being pushed away from all the muscles, joints, tendons and veins.
That’s just the way the piercer who put it in did it, I don’t know why. He’d done many of these implants before, even had one himself.
@Devilclarke Cool! My NExT is arriving in the mail in a few days, and I’ll be approaching piercers soon. So the different injection point piqued my interest
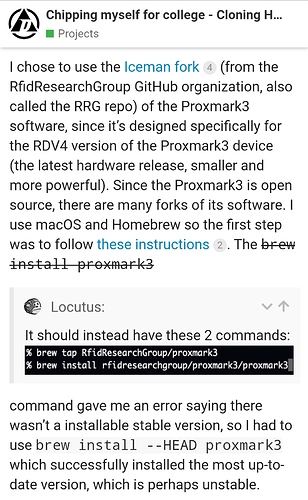
hey there, new to this, before I commit to injectables, im getting my head around the card cutting process. I have the pm3 easy. all installed and functioning. I need to learn about commands to clone / copy access cards (hf ) , I have an access fob for my apartment, and the desk ( hotel concierge ) has cloned / added my nfc/rfid ring ( nfc) so I can access my apartment. I need to learn how to copy the HID to other fobs. can someone hold my hand while I figure this out ?
We can definitely help you out, but also the PM3 will take you step by step.
Once you have tuned you antenna (if you haven’t already)
hw tune
HID could be either HF OR LF
For your sake, I hope it is LF
If you don’t know what frequency you are dealing with.
Do either
lf search
Or
hf search
When you get some results, let us know and we can tell you what to try next
Great thanks, it’s a hf mifare classic. iso14443-A. I have a blue fob that is 7 hex and a the DT nfc ( dual zone ) ring. the apartment concierge programmed it , it s 4 hex code. if it was a LF then I would have just used my 125kHz EM / HID / AWID Cloner.
Mifare classic tool for Android could work, depending on the coupling, if you use it in conjunction with a mifare classic 1k gen2 (if you want to use your phone; careful, it’s easy to brick) or gen1a (needs a Proxmark with magic commands, harder to brick, can be detected & rejected by some readers) card [or implant, xM1/flexM1 gen1a or gen2]. You can get your Magic Mifare cards from KSEC or similar.
Ah, see my confusion…
Well, the HID function won’t work when the HID is HID iClass.
Also, if you have a PM3 Easy, I would reccomend you using that over the Blue Cloner, (the blue Cloner is still good for what it is), but if you are still going to use the blue cloner, make yourself familiar with the password removal commands.
Also when you start using it on actual implants, you might want to consider Roscos great Blue Cloner Mod
I’ve heard that the blue cloner is a risk. which is why I went for the the proxmark3 easy. ( pff, yeah, real easy. its as easy as 98,000,000 simple steps. ha, even then a need to know what steps to take. and in what direction.
my question is simple. can the pm3 clone HF mifare 1k ? of so then how ?
Yes EASY ![]()
I don’t have one in front of me at the moment
Bit earlier when I said
So it will feed you options as you go, for example
We know it is hf
So first part is
hf
We also know it if Mifare
So the second part is
mf
So if you put in command
hf mf
The pm3 won’t know what you want, but it will give you you next command options, so you choose from the list and add in the next option into the string…
If you want to see all mf hf commands, type in
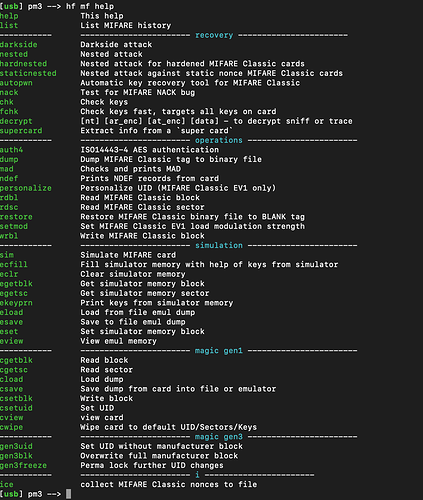
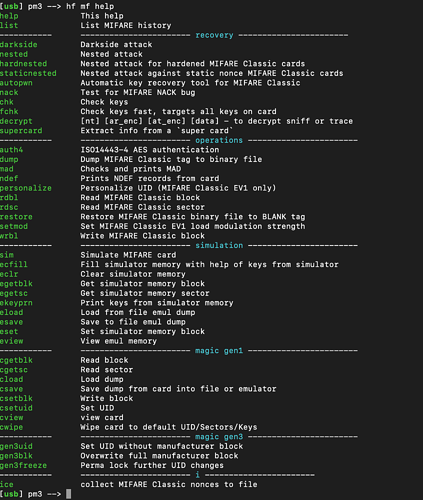
hf mf help
when I am at my computer I can feed you more info, but the step by step SHOULD be EASY enough for you to follow
hf mf help. gave me
one of my cards ( nfc tag - coded by building admin ) displays as
[usb] pm3 → hf search
![]() Searching for ISO14443-A tag…
Searching for ISO14443-A tag…
[+] UID: ## ## ## ## ## ## ##
[+] ATQA: 00 44
[+] SAK: 00 [2]
[+] MANUFACTURER: NXP Semiconductors Germany
[+] Possible types:
[+] MIFARE Ultralight
[+] MIFARE Ultralight C
[+] MIFARE Ultralight EV1
[+] MIFARE Ultralight Nano
[+] MIFARE Hospitality
[+] NTAG 2xx
[=] proprietary non iso14443-4 card found, RATS not supported
[?] Hint: try hf mfu info
[+] Valid ISO14443-A tag found
–
im not sure what to do from here to copy / clone from one card to another. ?
Okay, so you are on the right track
.
A couple of things.
It looks like you have an ultralight rather than a classic.
Can you do me a favour and scan with TagInfo
So when it comes to implants you will be looking at the FlexMN (Magic NTAG)
It is capable of emulating the Ultralight.
I don’t have one myself so I can’t help you much around specifics.
I do hope to get one in the future, but until then
Here is the link with some info
With regards to your Proxmark3 output above, you have done everything perfect, however, now it appears to be an ultralight, we have to tweak your commands.
As it says at the bottom of you post
So
HF
MiFareUltralight
Info
When it give you a result like you one above (may be different for the Ultralight commands) again I am not infront of my proxmark.
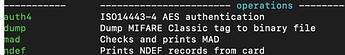
You would simply look at what you are trying to do (blue/green eg. Recovery or operations etc)
Then find the command (green) you want and add that to you previous command
So example for mifare classic
hf mf dump
Which would result in
Is that starting to make sense?
So if you can check you card with taginfo
Then you can try your commands with the
hf mfu commands
Yes thank you mate definitely making more sense now give me a couple hours and I think we might be good. Fingers crossed
ik so what im getting is I need to dump “hf mfu dump”. then load that dumped file back onto a new key ?
Sorry again, this is just my morning catchup, and I’m away from home for another couple of days and I don’t have PM3 with me.
I’m not super familiar with ultralight commands
Hopefully somebody can give you the exact command line.
But if it is similar to Mifare Classic it will be something like i.e. (don’t use these commands they are off the top of my head)
The dump command requires a bit more work to get the keys, but
If you simply want to write a new NUID
It will be something LIKE
hf mf csetuid XX XX XX XX w
(The w is to wipe the card)
I would try and find you the commands here on the forum, but “recently” there has been some syntax changes and I may end up giving you the old commands that will probably just give you errors.
That is why it is better to just follow through what the PM3 is prompting you to do step by step.
Sorry I haven’t been much help, but hopefully somebody can jump in to give you more specifics