EDIT: See 6th post in this thread for a better option than what’s in this post.
Link for the lazy to the 6th post: Desktop OTP display using Yubico Authenticator and Apex Flex - #6 by pockybum522
Original post:
Hello All,
Got a tip from Amal when I asked about options for showing OTP codes on a PC like I enjoy doing with my Yubikey.
He suggested modifying the AID in the Yubico OTP app, and it worked, so I figured I’d write up instructions for anyone else who wants to get codes on their PC. I have so far tried this on Windows only, but I am guessing the process is similar for other OSes.
Process:
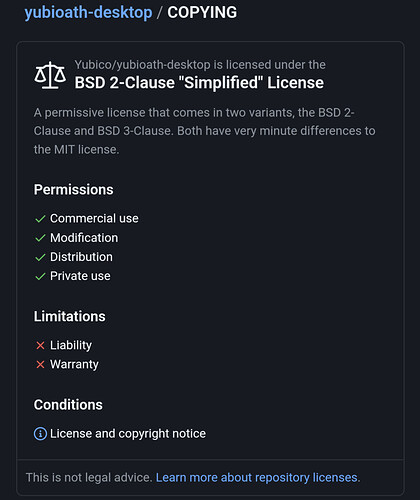
I installed the latest release of Yubico Authenticator from:
(64 bit, but since we’re just modifying scripts I’m guessing 32 bit will also work fine.)
Once installed, I made a backup copy of C:\Program Files\Yubico\Yubico Authenticator\ and since this is a quick and dirty mod to make Apex work it also means your existing Yubikey won’t, so until we get a cleaner solution, you’ll also want the unmodified copy around for if you still need Yubikey compatibility.
Note that this is with VivoKey OTP applet in Fidesmo.
You’ll want to edit C:\Program Files\Yubico\Yubico Authenticator\pymodules\yubikit\core\__init__.py in notepad++ or VSCode. Around line 83, there should be: OATH = bytes.fromhex("a0000005272101")
Change this line to read: OATH = bytes.fromhex("a0000007470061FC54D5")
Of course, be careful to maintain indentation, and don’t tab to make the indentation, looks like this file uses spaces to indent.
You can see my file, modified, below. My cursor is on the modified line, and the original line below it is commented out.
Save that, close out the file, and open C:\Program Files\Yubico\Yubico Authenticator\yubioath-desktop.exe in the modified folder. Note that for some reason, my yubioath-desktop.exe seems to need to run with admin privs.
This is off my Apex Flex:
And it shows up as:
Meta/Semi-related Info:
My NFC reader is “Advanced Card Systems Ltd.” USB NFC Reader ACR1252
P/N: ACR1252U-M1
I purchased it on Amazon like a year or so ago.
Note that you have to set a filter in the Yubico Authenticator app under:
- Settings > Custom Reader
- Click Enable Custom Reader
- Select your reader
- Click “Use As Filter”
- Click Save
Only then will the Yubico Authenticator app be able to use the USB reader.
DISCLAIMER: YUBICO DOES NOT SUPPORT ANY OF THIS. NOTHING FROM DT IS AN OFFICIAL YUBIKEY, DUH. DO NOT BOTHER YUBICO IF THINGS DON’T WORK OR BREAK, DOWN THE ROAD.