Hi all biohackers!
First a disclaimer: I’m a total newbie in RFID/NFC so I’ll certainly say something stoopid in this post. My goal is just to share my experience and experiments and and hopefully learn a little bit more with yours feedbacks.
So first: I have an xNT implants since the 21 November 2014.
For the French users who are interested I got my implant installed by Artpellis in France Fontainebleau 77 (Last time I checked they still wasn’t listed on https://dangerousthings.com/partners)
Here is their Facebook page: Redirecting...
They took the time to read the professional guide provided by Dangerous Things and they did a perfect job on installing the implant. I definitely recommend them.
In the past 6 years I’ve acquired an absurd quantity of Chinese RFID readers and was always disappointed in the reading power (certainly due to bad antenna design). The best one so far is this one:
His friendly name is « KR601-IC »
Do not confuse him with his little cousin « KR601-ID » as this is the 125KHz version.
It’s 12V input and all « PIN » are all 5V.
It’ll consume around 22mA on average in standby and will goes up to 33mA when reading a tag.
- Red: 12V+
- Black: GND
- White: Wiegand Data « 1 » (when this line is pulled LOW that mean a binary 1)
- Green: Wiegand Data « 0 » (when this line is pulled LOW that mean a binary 0)
- Purple : Buzzer (when this line is pulled LOW the buzzer will buzz)
- Grey : Green LED (when this line is pulled LOW the red LED will be green)
- Yellow : Wiegand 26 (when this line is pulled LOW Wiegand Data format will be 26 bits long instead of 34)
With this reader I was able to get readings with my xNT implant as far as 1cm of distance when I’m properly aligned with the coil.
The RFID Diagnostic Card start lighting up at 8cm of distance
And max LED brightness is at 6cm from the reader
The 13.56MHz X Field Detector start blinking at 2cm of distance
And max LED brightness is at 1cm from the reader (on the edge of the reader)
This reader is capable of reading my xNT tag from 1cm of distance
Keep in mind that when this reader will be mounted on a concrete wall or a metal door, reading performance will be worst. Mounted on a metal poste I couldn’t get any reading with my xNT implant so I had to offset the reader.
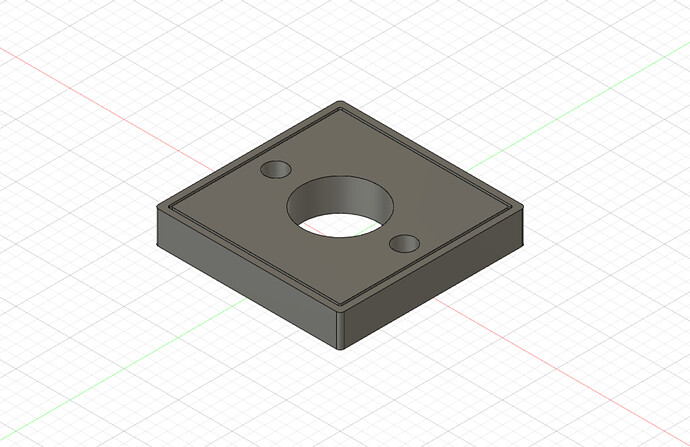
I’ve made a 3D print that will offset the reader 15mm from the mounting surface.
For those interested here are the STL / STEP files
RFID_spacer.zip (24.5 KB)
You can see the final result here
With this print I can now achieve similar readings as if the reader was just on the test bench.
This reader will output the card data using the Wiegand format / protocole.
For the next part I’ll use a Proxmark3 Easy to simulate an ISO/IEC 14443 type A tag to avoid spoiling my xNT UID, but the results will be exactly the same as using an NTAG21X.
I’m using the Iceman release v4.9237
I’ve updated the firmware of my Proxmark3 Easy using this guide
I’ll use this command: hf 14a sim v t 2 u 04420815ff0484
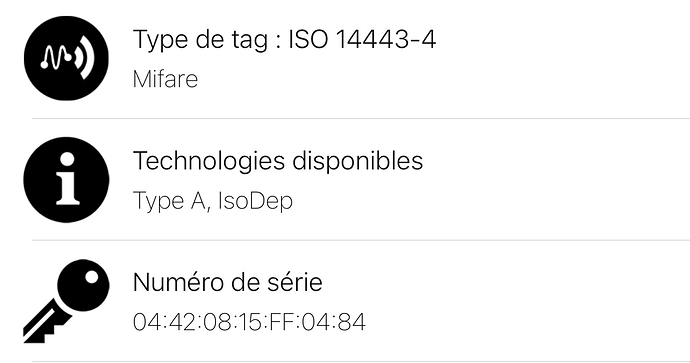
to simulate a tag with the following serial: 04 42 08 15 FF 04 84
Using my iPhone I can check if the 7 bytes UID are correctly be sent
App used: NFC Tools
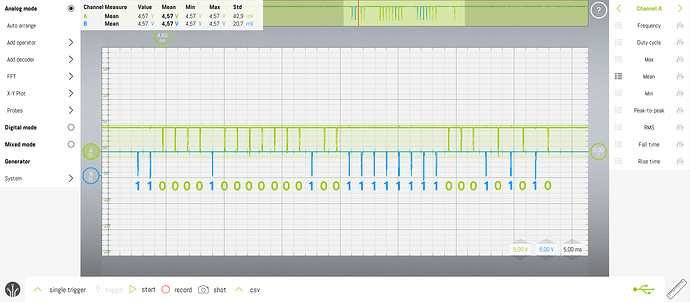
Let’s try to read the Wiegand output from the reader with an oscilloscope:
Channel A (green) is DATA 0 and channel B (blue) is DATA 1
The reader in the default setting (Yellow cable floating) will output this Wiegand 34 format.
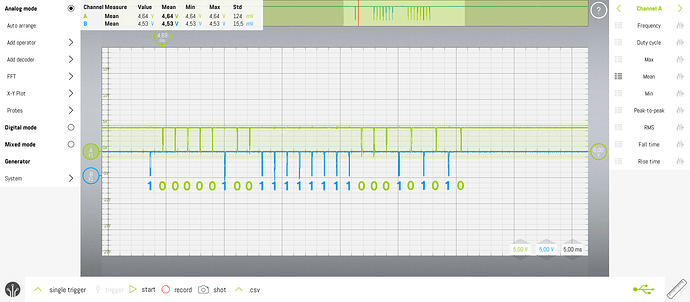
For comparaison this is the output when the Yellow pin is pulled LOW
Let’s decode the Wiegand 34 output: 1100001000000010011111111000101010
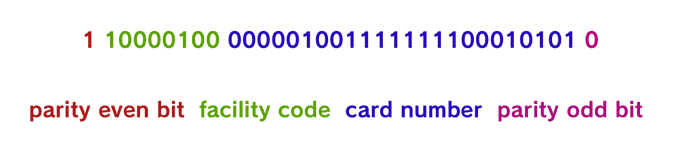
Assuming the reader is properly implementing Wiegand standard we should have the following format
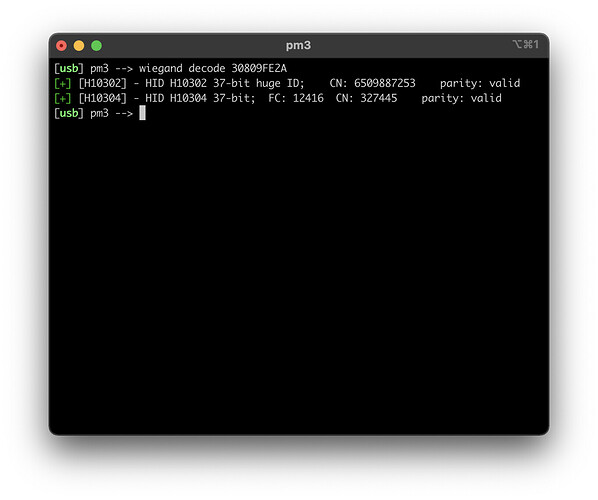
Converted to hex: 30809FE2A
I can decode this raw data using pm3 but it seems that our Chinese fellow didn’t used any known standard / format used in pm3
pm3 detect this tag as a 37 bit Wiegand.
Never-mind this « Chinese Wiegand » format can be easily reverse engineered as they simply used 2 parity bits and then the UID
Lets ignore the 2 parity bits and convert the binary to hex:
10000100000001001111111100010101 = 8404FF15
There we have it. It’s the last 4 bytes of our serial (but in reverse)
This is really annoying since last 4 bytes of most tags that I have are the same…
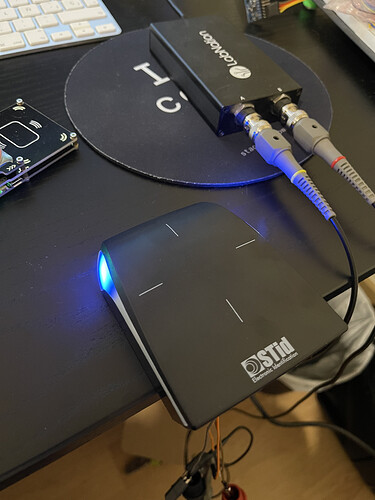
So right now I’m trying to get my hands on some more professional readers (like STid) but they don’t want to sell you any readers if you are a simple hobbyist.