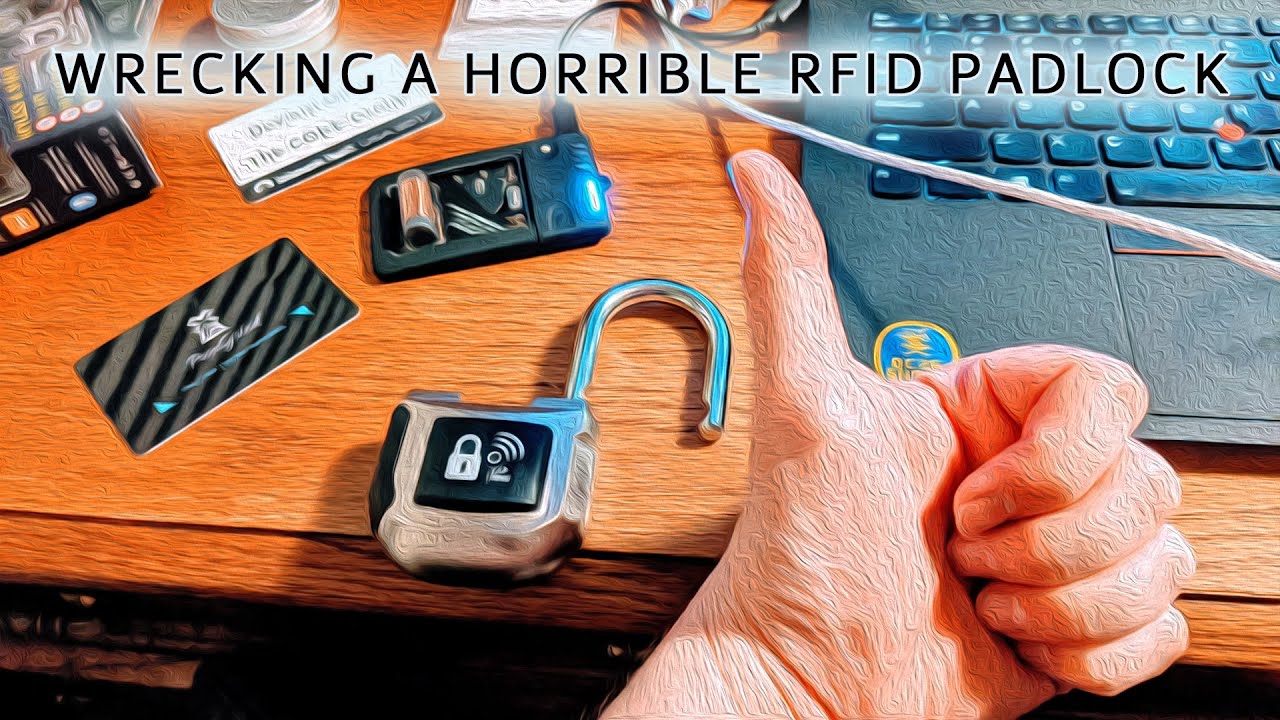
Deviant Ollam just released a interesting video about the lock, might be one to avoid if people are intending to secure anything important.
Well… the issue he is describing is true of all the systems that are based on the UID… So for example the xAC is just as insecure as is the KBR1 etc. I would be more interested in if it is easy to bypas with a shim etc.
I was more thinking of the fact it was getting stuck in unlock mode etc than the UID issues.
Likewise, but It does look like the shackle has ball bearing cut outs rather than locking pawls, so not too likely for a shim, but stand to be corrected.
However, I would next try a magnet solenoid attack, or an electrical bypass short.
Personally I would stay away from an electronic attack as it holds an activity register on the App ( I am not sure if it does this for only Bluetooth or if it also holds for RFID, so you may get away with accessing via clone or emulation attack, but it may leave a bread crumb.
I am looking forward to his next video of the tear down.
At the end of the day, if it suits your purposes and you are aware of the vulnerabilities, then it may be a “good” lock for you…
He harps on about how bad UID-based authentication is. And he’s right of course. But that’s hardly news: ALL low-frequency tags work that way, and ALL NFC products of any kind that want to be compatible with as many transponder types as possible (including a certain login software made by yours truly ![]() ) default to using only the UID for authentication - which is essentially the equivalent of emulating legacy low-frequency tags with NFC tags.
) default to using only the UID for authentication - which is essentially the equivalent of emulating legacy low-frequency tags with NFC tags.
If that’s his main beef with the product, then he must be livid each time he gets into one of the billion kajillion office buildings in the world that still use LF tags ![]()
The real problem is that this lock only uses 2 bytes out of a full UID. That’s the equivalent of having a padlock with 65,536 possible codes. Most coded mechanical padlocks provide only 10,000 possible codes, so 65,536 isn’t that terrible all in all. But why not use the entire UID? In a mechanical lock, it’s understandable. But with a firmware, that’s really stupid.
Then again, it’s just a padlock. Use it for low security applications where all you want it to do is keep honest people honest, like lock a gym locker full of dirty underwear, and the convenience probably outweighs the poor security.
It also probably helps because the average person isn’t as informed about RFID/NFC. Security though obscurity sometimes works!
Exactly. Cloning RFID or NFC UIDs is trivial for pen testers, and for just about anyone with a passing interest in the technology.
But practically, the reality is, who the hell walks around with a conceiled scanner and a Proxmark? More importantly, what’s so important about whatever is secured by that LF or HF tag that makes trying to discreetly scan it, then making a clone of it, worth the effort? Not to mention the added difficulty of doing that with an implant, without the implant wearer noticing…
Unless you attend DEFCON - in which case you deliberately put yourself in a setting ripe for that sort of shenanigans - or you’re in a relationship with a technologically-savvy partner who wants to do you harm, for most people with mundane security needs, I don’t see the use of dumb tags as a problem.
It’s probably why they’re still in use by the millions around the world to secure access to buildings.
I do want a proxmark implant at some point though! It can go in my other leg, lol.
Uhh, I’m sure you got mixed up but that would be impossible.
What is impossible?

I mean
That seems possible. The read range would suck though. @Moonman0922 is already ment to have the PegLeg in one of there legs iirc.
How would you power it though?
Well the peg leg uses a Qi charger, so something similar likely.
Seems wildly impractical when you can toss a giant antenna and a battery in a bag
I have a feeling practicality is not the key factor for those types of projects ![]()
Truuue
I think it is more something no one can take from you. If enough people have that device, there would be no need for centralized internet correct?
If a peg leg showed up to a protest, people could still communicate to each other if the cell networks got shut.
There are mesh network communication apps. An old one I remember was called FireChat. No pegleg required just enough users at say a protest.