Hey everyone, been a while since I’ve posted a topic here ![]()
These days, more and more of our ‘private’ data is more accessible to third parties than ever. Often people’s views of privacy fall into two categories - “I have nothing to hide” and “everything is terrible, I don’t exist online”. In this topic, I’d love to instead start a conversation around it really being a spectrum, where everyone can improve their privacy somewhat.
Background
Why is privacy important, even if we supposedly have nothing to hide? In essence, it boils down to informed, explicit data sharing is great, but when consent is implied or not informed, issues arise.
Think of it this way - if you truly have nothing to hide, put all of your CC details in this thread ![]() . What about your address? The last adult content you consumed?
. What about your address? The last adult content you consumed?
And if you’re happy to share all of the above, great! More power to you! But would you share someone else’s data in this thread without consent too? Your parent’s phone numbers? Their addresses?
All of this data could likely by collected from our day to day activities online.
Now none of this is intended to be scary - we get some amazing things by sharing our personal data, but we should also consider our level of risk and see what else we might want to implement:
The basics
-
The obvious one - don’t do seriously illegal things in public / semi public relatively insecure places
-
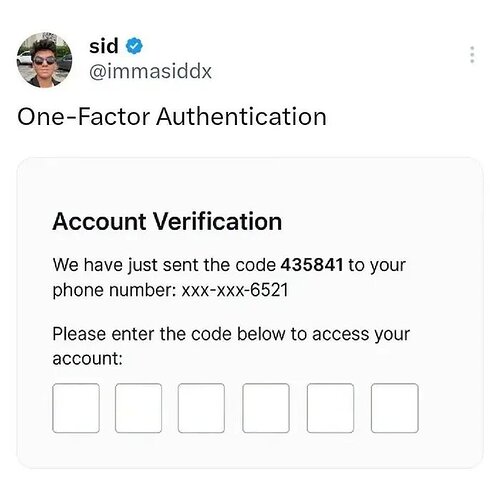
Implement some general privacy practices - check if you’re reusing passwords and usernames, consider setting up separate email accounts for certain things, improve your work / personal separation
-
Be aware of the difference between ‘secure’, ‘encrypted’ and ‘private’ - just because something is secure doesn’t mean only you can access it for example
-
Use an adblocker - this is actually something that is recommended by the FBI (yes, really - or at least by some US gov department)
Some reasonable risk mitigations
-
If you are slightly concerned about an application, some midrange suggestions are:
a. Android: use a work profile / app like ‘Island’ to separate personal data
b. PC: use an open source browser + good ad blocker + a web version where possible - can even usually get notifications using this approach
c. Minimise personally identifiable information shared, and ideally don’t use unencrpted DMs for sensitive data - look at more secure messaging (Signal etc.) -
Use a VPN - but be aware of exactly what they can and can’t protect you from, and pick one that stores as little information as possible
More extreme risk mitigation
If you’re concerned enough about certain applications etc. to desire to run them in a virtualised environment, here are some suggestions:
-
Look into Tor / I2P, but be aware of their limitations / they can be significantly slower than a VPN
-
Have a work phone, a secure communication method (LineagoOS? Graphene? Linux based mobile?) and if you can’t live without social media, a secondary ‘normal’ smartphone
-
Have multiple lightweight sandboxes setup for various companies / purposes
-
Create PGP keys with a public rotation scheme and use that for secure messaging where needed
BTW, anyone who wants more information on privacy etc., let me know, I am most certainly not an expert but I may be able to give some initial direction and am always looking to learn more! Looking forward to hearing everyone’s thoughts ![]()