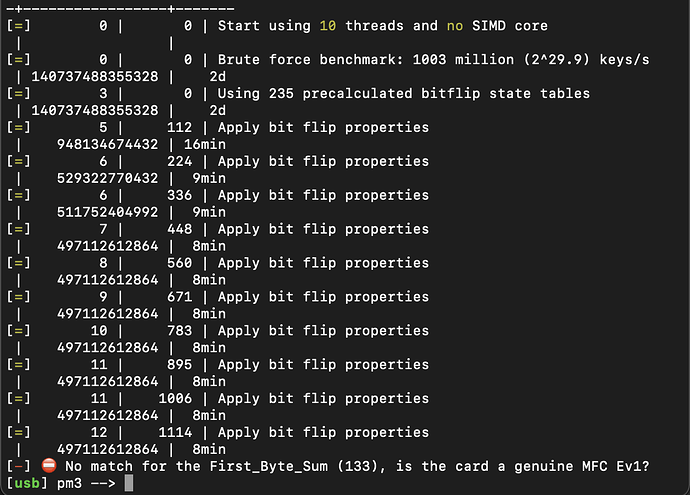
I keep getting this error, can someone please help me? This was after hf mf autopwn
I was getting something similar, and I can’t make heads or tails of it except mine is like 10 pages long of it just trying the same code over and over
Can you confirm your firmware version and client version? It should be on the client launch screen when starting the pm3 client.
Also are you sure you’re working with a mifare card? Can you show what hf search outputs?
Not sure if talking to me or not… gimme 20 minutes and I’ll get everything set up to scan it some more and post screen shots of what it do
ok setup,
Ill do a hw tune , hf search, hf mf autopwn and post
its worth noting, my pm3easy wont find the iso card if it is directly underneath… needs to cut the iso card in half just like implants
start up, and HW tune
[=] Session log C:\ProxSpace\ProxSpace\pm3/.proxmark3/logs/log_20220924.txt
[+] loaded from JSON file C:\ProxSpace\ProxSpace\pm3/.proxmark3/preferences.json
[=] Using UART port COM3
[=] Communicating with PM3 over USB-CDC
8888888b. 888b d888 .d8888b.
888 Y88b 8888b d8888 d88P Y88b
888 888 88888b.d88888 .d88P
888 d88P 888Y88888P888 8888"
8888888P" 888 Y888P 888 "Y8b.
888 888 Y8P 888 888 888
888 888 " 888 Y88b d88P
888 888 888 “Y8888P” [ ]
[ Proxmark3 RFID instrument ]
MCU....... AT91SAM7S512 Rev B
Memory.... 512 Kb ( 58% used )
Client.... Iceman/master/v4.14831-603-g76da953bc 2022-05-20 04:37:36
Bootrom... Iceman/master/v4.14831-603-g76da953bc 2022-05-20 03:37:27
OS........ Iceman/master/v4.14831-603-g76da953bc 2022-05-20 03:38:03
Target.... PM3 GENERIC
[usb] pm3 → hw tune
[=] ---------- Reminder ------------------------
[=] hw tune doesn’t actively tune your antennas,
[=] it’s only informative.
[=] Measuring antenna characteristics, please wait…
[-] 9
[=] ---------- LF Antenna ----------
[+] LF antenna: 23.17 V - 125.00 kHz
[+] LF antenna: 22.18 V - 134.83 kHz
[+] LF optimal: 25.88 V - 127.66 kHz
[+] Approx. Q factor (): 7.6 by frequency bandwidth measurement
[+] Approx. Q factor (): 7.5 by peak voltage measurement
[+] LF antenna is OK
[=] ---------- HF Antenna ----------
[+] HF antenna: 16.45 V - 13.56 MHz
[+] Approx. Q factor (*): 4.8 by peak voltage measurement
[+] HF antenna is OK
(*) Q factor must be measured without tag on the antenna
[+] Displaying LF tuning graph. Divisor 88 (blue) is 134.83 kHz, 95 (red) is 125.00 kHz.
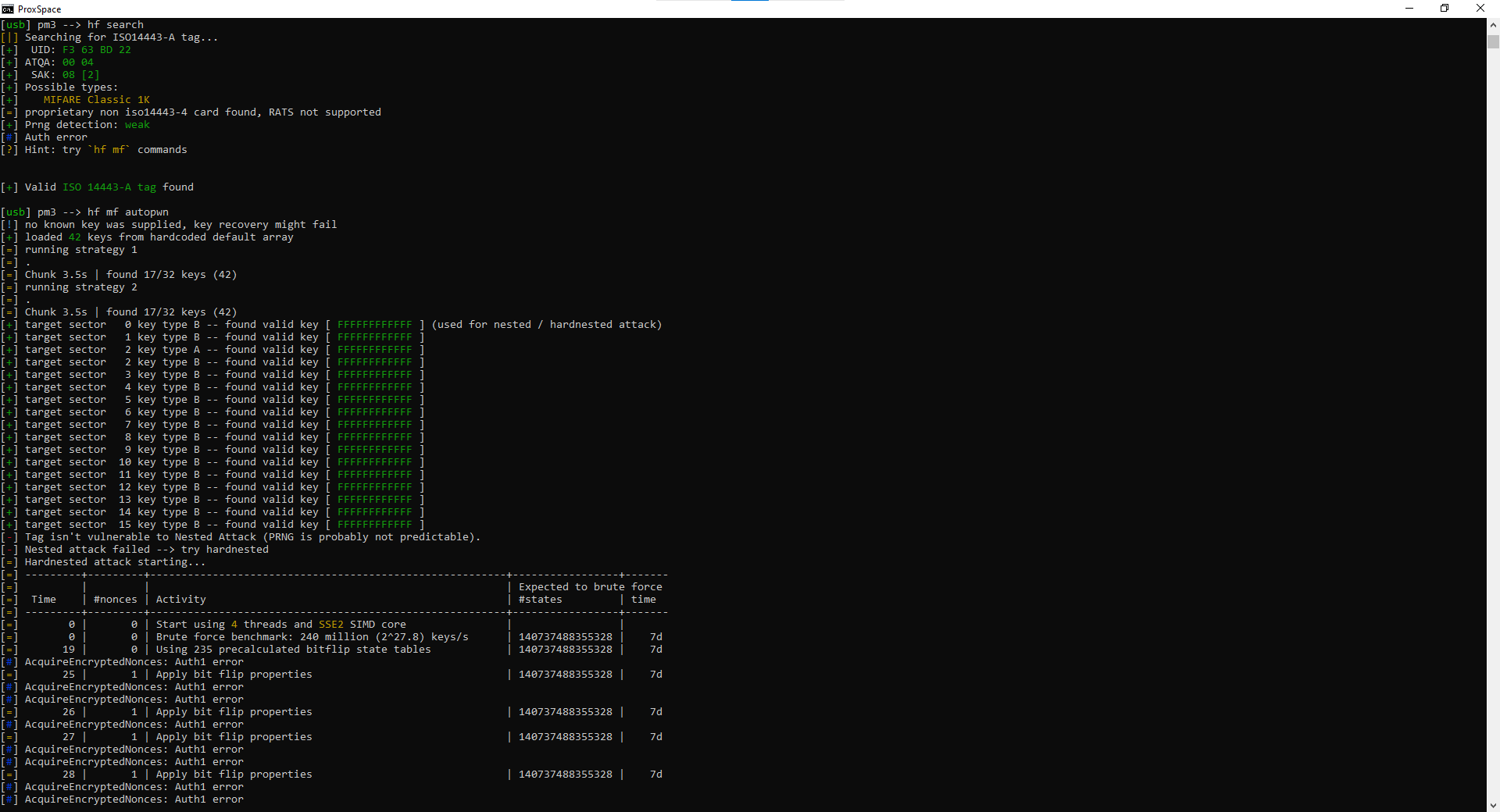
HF search
[usb] pm3 → hf search
[|] Searching for ISO14443-A tag…
[+] UID: F3 63 BD 22
[+] ATQA: 00 04
[+] SAK: 08 [2]
[+] Possible types:
[+] MIFARE Classic 1K
[=] proprietary non iso14443-4 card found, RATS not supported
[+] Prng detection: weak
[#] Auth error
[?] Hint: try hf mf commands
[+] Valid ISO 14443-A tag found
hit a character limit and can’t post more replies so screenshots it is
here is the opening
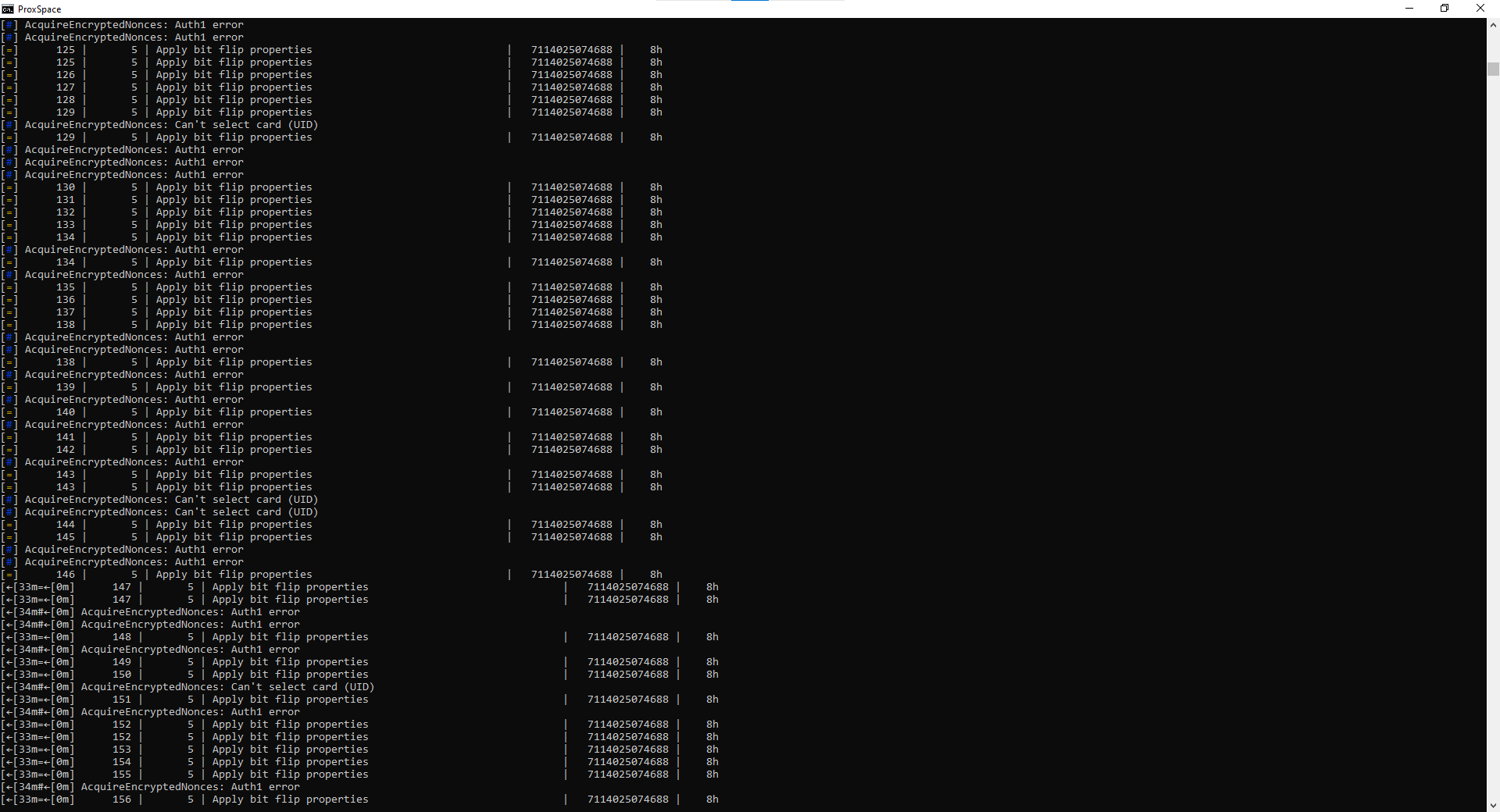
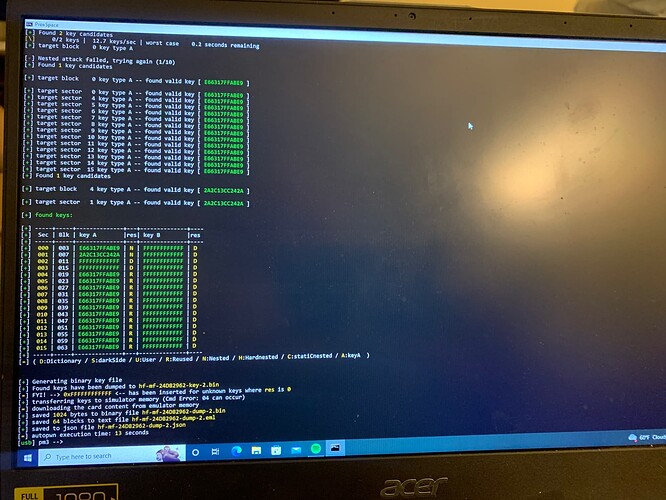
this went on for some time, then it changed a bit
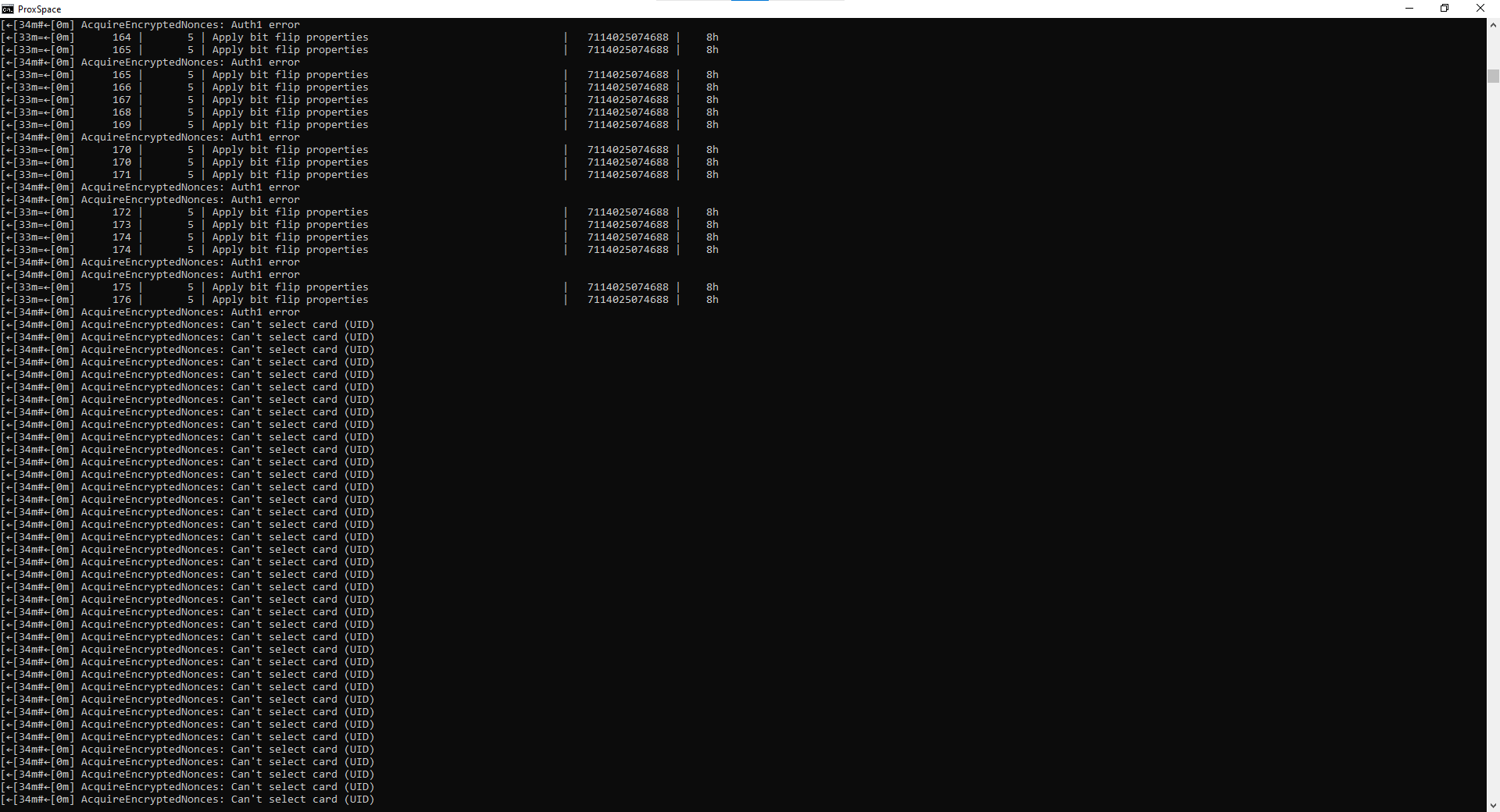
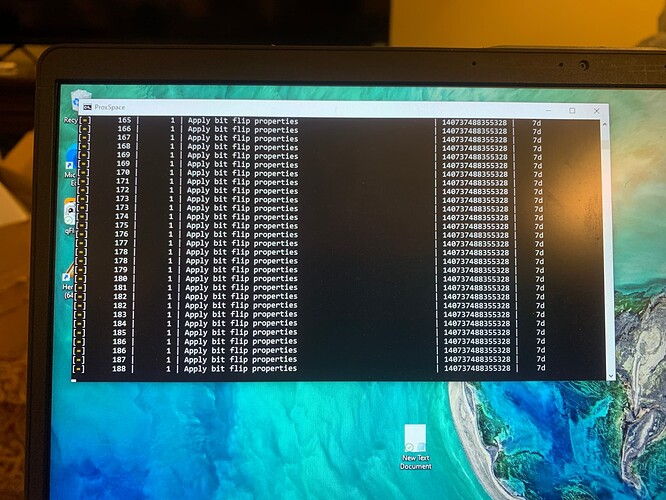
then it went to hell and stopped registering
Ok so the question is…is that sector burnt or just protected by access bits and keys? Chances are it’s burnt. Would you happen to know if that’s true?
It’s a brand new mifare card from a hotel ![]()
Interesting. Might be burnt but who knows
When it says auth error looking for nonces
Was that actually working? Or just repeatedly erroring out?
I’ve tried running it again, and it won’t stop like it did before but I don’t know what the bit flip and auth1 error stuff mean
I’m pretty sure auth1 error is just exactly that… sending the auth command and getting an error response.
The thing about it is that I don’t know if a burnt sector is going to return anything but an error. I don’t think it has a specific error return code that is different for a burnt sector than one that is just not authenticating because yours passing the wrong key. Basically I’m saying I don’t think there’s way to tell if a sector is current or locked by sending key authentication commands. The return is likely going to be the same error code.
I’m kinda confused why it would be burnt out
Got it from the hotel, used it for 2 days and then it went into my “learn to copy mifare” bin
My occans razor thought is I’m just doing something wrong before assuming it’s burnt out
Sure but Amal’s razor says it’s prob the card. Either it’s not a true mifare classic card or the sector is burnt. You’ve got the correct firmware and client, the commands are correct, and you have keys for the other sectors. Unless somebody broke the hard nested crack code in the proxmark firmware, it’s most likely the card. That’s the simplest explanation.
Of course this might not be true. There might be something wrong with the proximark firmware such that two people have had problems accessing a particular sector on a true mifare classic chip. That is possible, just not the simplest explanation.
I have another mifare from a hotel, but it reports it’s a different type of mifare… I’ll try to post what it says in a second
(I can’t get it to tell me what it said before… so maybe it was a fluke)
It looks like the other hotel card autopwn’d immediately and correctly
Could the hotel be semi bricking cards as a security measure?
Could I have burned it out doing something wrong?
I tried this once during my stay and the card kept working for w/e that’s worth
I ran a hf tune and very carefully put the iso in the strongest posistion and tried autopwn again
It’s not throwing the auth error code, is that better or worse?
In my poking I’ve found 2 things that I don’t understand that could be parts of the equation… there was some issue with autopwn and nested attack with iceman… but it looks like it was fixed?
If I try to initiate the nested attack manually it fails saying it can’t find the .bin file…
(I have no idea what the nested attack IS, just that proxmark seems to try other stuff before hand and eventually escalates to this… something online had said they couldn’t get autopwn to work but running it manually worked)
So good chance I’m doing something wrong or have no idea what I’m doing, but maybe something is wonky?
Additional potential flag…
During w/e the proxmark wants to do, I can’t exit or quit or anything… and I’m forced to close the client entirely … not the end of the world I guess
Afterwards windows ejects and reconnects to it… so maybe the hardware is getting locked up?