Started this project last night. All of the parts have arrived except for the iclass readers which haven’t shipped yet.
First off, huge props to Compgeek for turning me on to the Wemos D1 Mini. This project will be based on that board. Super small, low power draw, and more power than I’ll ever need for this project.
I chose to go with the iclass SE because my xEM is flashed often for various purposes. However, the xNT UID always stays the same. So basing my scanners on 13.56. My previous AWID project was more a research project that an actual use case.
The code from the previous project was very easy to change for the Wemos D1 board. The biggest changes were using the correct 8266WiFi.h file, and I had a few competing files of the same name. Also, the pins are referred to in a different number scheme, so I had to convert the INPUT/OUTPUT pins to use the Wemos constants of D2 and D3 instead of 2 and 3. And a few tiny changes like the way functions return values.
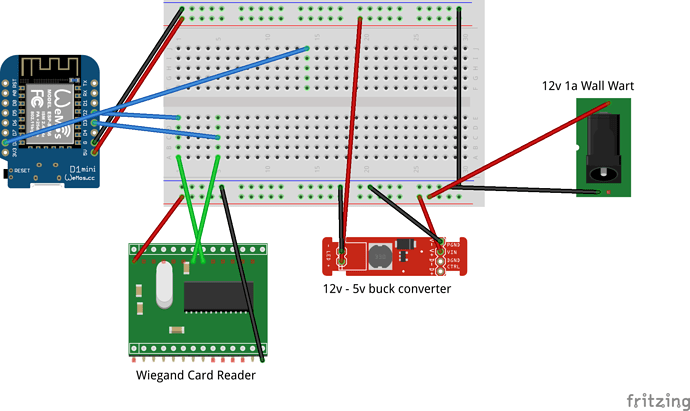
Parts list:
Wemos D1 Mini
12v 1amp wall wort
Adjustable step down buck driver
Used HID iclass SE(NOT THE MULTICLASS)
22AWG 8 conductor shielded cable
Many products were purchased in multi packs, so the price breakdown per unit is $33 not counting the cable as the price differs greatly based on length needed. $22 of that going to the used iclass SE.
There are a wide variety of Chinesium 14443a compliant scanners. However, in addition to reviews stating poor range, the cables are not shielded and there isn’t even a shield wire. So I paid the few dollars more(literally $4 more) for the used iclass SE.
The readers will have the best range with the higher voltages. So the reader will be powered off the full 12v from the wall wart, and the Wemos will be powered off the adjustable buck driver. I spent more on the adjustable buck drivers because it’s a multipack, and the left over units are much more useful with the wider range of input and output voltages, and they are more efficient. Could have saved a few dollars going with the cheap 12v to 5v linear buck converters.
The readers will be placed outside at the 2 doors. My house was built in 1958, so there is only 1 outdoor electrical outlet. But I do have a basement with direct access to the 2 locations. So the Wemos will be in the basement, and the shielded cable will be ran out to the readers. Since the cable runs will be roughly 10ft, I feel a lot more confident using shielded cable.
Much like my previous AWID project, this project connects to my IoT wifi network and passes MQTT messages to Home Assistant. The biggest change to this project is that the Wemos are programmable over the network. So I added the code to allow for network flashing for ease of upgrades. With the new Wemos boards, I’m already experiencing massive performance gains. With the aged Duemilanove, it took about 15 seconds to boot, connect to wifi, then connect to MQTT. This new board does the same in 2 seconds.
Hopefully, the next post will be a success with a demo as I believe all I have to do is swap out the AWID reader for the iclass reader. But if not, it will be more of a build log.