So here goes!
Below I am going to try and outline my experiences with the xEM implant and Chinese cloners in the hopes that it will help some of the community. I am no expert - just a guy that likes to fiddle in my spare time. I got my xEM implanted some months ago and after cloning my work HID card to the xEM with one of the dreaded Blue Cloners I have been on a war path even since to understand the technology properly, unlock my implant and possibly help some other people unlock their implants.
Firstly I want to thank Skeeve Steevens, Shanti and the team at Chip My Life for both convincing me to get the implant done and providing me with a lot of the tech needed for R&D. If you are in Australia I highly recommend getting your gear and even booking your installation through them! Check them out at:
Secondly thanks to Amal for sending over some xEM’s to test on along with various other bits and pieces. And thanks for generally supporting the R&D of the community in the way that you do!
Last but not least, thanks to James Campbell for your input along the way and bravely letting me do the first real testmode unlock on your hand.
Some Assumptions:
I will try and explain everything in detail but if I were to cover absolutely everything this post would turn into a small book. Therefore, the below assumes that the reader have some basic understanding about the data structure of a t55xx chip and what data is stored in each page and the successive blocks in that page. Also you should have a grasp on proxmark lf t55 operations. I suggest checking out the following to if you need a refresher:
and maybe have a brief read through the ATA5577C datasheet:
https://dangerousthings.com/wp-content/uploads/xEM_Atmel-9187-RFID-ATA5577C_Datasheet.pdf
And probably the proxmark3 command reference. Play with some spare t5577 keychain fobs, break them, un-break them and learn as you go.
We are going to talk about two well-known Chinese cloners, the proxmark3 and the beginnings of some custom coils for the proxmark3:
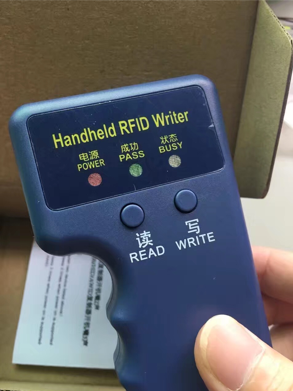
Blue EM / HID Cloner:
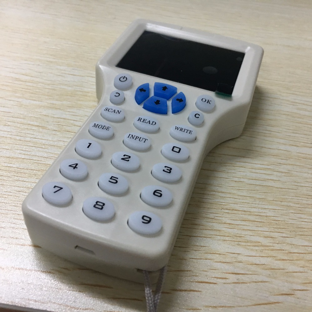
White Multi-Frequency Cloner:
I will begin with briefly covering what has already been discovered. We know that when writing to the xEM (or any t55xx chip) certain Chinese cloners set a password in block 7 of the chip and the password enable bits in block 0. So far people have worked to sniff or acquire the password in order to unlock their chip & help others in the community. I was lucky and used a blue cloner with a known password. Some were not so lucky and used one of the white handheld cloners pictured above, which lead a lot of people to think their xem was perma-locked to that cloner as even a proxmark3 with the correct password would not unlock the chip - more details on this later.
Let’s go over each cloner in a bit more detail!
The Blue Cloner:
From what I have seen after getting to play with about 8 different units from various sellers & sources:
-
The coil quality and component quality in these devices varies a huge amount. This means that some people have units that work very well and almost always consistently read and write to an implant (I have one myself that works consistently at roughly 2cm away from my skin), note that you still need the implant in roughly the right orientation (more on this later).
-
There are a lot of very subtle variations of this device being sold, plastic type, slight mold size change and some vary slightly in color - they all have the same circuitry, but some have different firmware that either does just HID mode, just EM mode or both.
-
Most if not all of these blue cloners set the same password: 51243648, and can be unlocked with a proxmark3. Even the with the variations I have seen the password remains the same - I have not seen one that sets a different password.
-
People previously thought that some of these set a different password BUT, I propose that some are having issues unlocking due to bad RF coupling with the stock proxmark3 coil.
The White Cloner:
-
The coil / component quality in these far surpasses the Blue Cloner and is a lot more consistent. After playing with about 4 of these they all read and wrote to the xEM from centimeters off the skin.
-
These ARE multi-frequency. You can even “kind of” change the UID of a Chinese backdoor mifare card in the displayed IC mode" - actually High Frequency mode.
-
The Windows based software supplied on the device does actually work to crack and clone a mifare classic card with some variation of the hardnested attack.
There are three main “English Version” variations of this unit that I have seen so far:
1. Older than 2015
If you have one of these the buttons will light up BLUE!
a. Reads the card data correctly i.e. for a HID card with a facility code of 150 and a card number of 3000 the screen would read 0015003000.
b. Has a slightly deferent startup screen / firmware than never models BUT if you look closely are actually running
newer version of the firmware? Huh?
c. Coil performance is definitely not as good as newer revisions
d. The input button is actually useful because you can properly input the facility and card code correctly.
2. Newer than 2015
If you have one of these the buttons will light up WHITE!
a. Does not read the card data correctly i.e. for a HID card with a facility code of 150 and a card number of 3000 the screen would read some nonsense like 81504055. (have not been able to figure out what the conversion is - seems totally nonsensical and likely something that was put in place by the manufacture for fear of legal issues from HID global LOL)
b. Coil performance is AWESOME! I mean seriously awesome! Clean reads / writes with the xEM every time!
c. The input button is useless as the device does some crazy conversion that as stated above is nonsensical and so far, impossible to figure out. So really this device is only good for cloning.
3. Rip off FAKE cheap version (anything less than about $60-70 AUD is usually one of these):
a. Only works for EM / ID cards, no high frequency and no HID from what I can gather (have not had one to play with yet).
b. No high frequency functionality as it’s a rip off device
c. Just don’t buy one, it’s not worth it.
-
Again, most if not all of these cloners set the same password AA55BBBB.
-
These cloners have a HUGE issue when used in the displayed “125khz ID” mode which in actuality, is EM410x mode that prevented a lot of people from being able to unlock their implant. This issue, and fix that I have found will be outlined in detail further on.
Now that we are a bit more familiar with the devices let’s look at some of the issues that I have faced, and found solutions for.
A few things to note:
-
The stock proxmark3, proxmark3 RDV2 and proxmark3 easy antennas are NOT designed to work with the cylindrical antennas in our little xEM’s. This causes a few issues with accuracy when we try to read / write to the chip. This has been outlined in other posts, so I won’t go into great detail about write tearing, but I will offer a way to help prevent it.
-
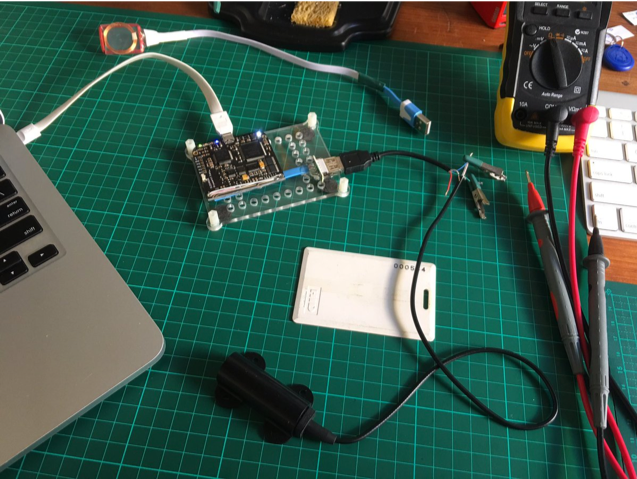
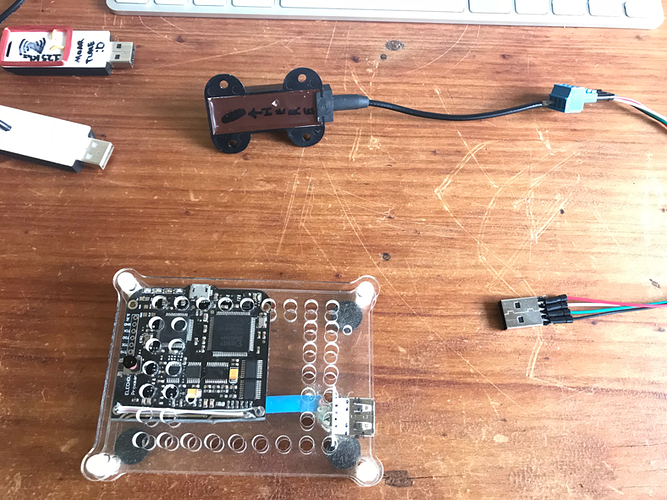
I have the proxmark3 easy board, that is the cheaper version. BUT have cut the built-in antennas cleanly off the main PCB so that I can attach my own custom antennas via USB port - allowing me to do some experimentation. Pics Below:
ISSUE #1 - IT JUST WONT WRITE 9
This problem happened to me for about 2 weeks when I first got the proxmark3 and was using the stock coils. I was fairly certain I had the right password for the Blue Cloner used to first copy a HID card to my xEM, but still nothing was happening when trying to unlock the chip.
Trying to set the Block 0 configuration so that it was not password protected just did not work, I had the right commands and the right password but was not getting results, the chip remained locked. I thought shit, maybe I got a cloner with a different password. After another week-long adventure, learning to sniff the password when the cloner writes to the chip. I managed to sort the data and get a password, SHIT it was the same known password from other cloners (51243648) - SHIT!
After much digging and reading online I noticed that Amal had used the coil from the xEM access kit on a proxmark3, GENUIS! I got that same coil, made a usb plug for the proxmark3 and managed to write the correct settings and unlock my chip. Hooray I thought it was all over!
Not quite…
Keep in mind that this antenna is not designed to work with the proxmark3, nor has it been tuned even closely to what it should be. So, when issuing a hw tune you’ll be under 10v with a long cable.
I then Wrote my xEM to an EM410x ID with that same coil to use with some equipment at home for testing, all went well… Until I had to re-write my HID ID back later that night so that I could get in to work the next day. I tried to write, nothing, nothing again, more nothing, Its still in freaking EM410x mode! Argh! WTF!
I shortened the cable between the coil and proxmark and used a lighter gauge wire in an attempt to get more power. This worked, and I was finally able to write the xEM back to HID mode. PHEW! Coil tuning matters more than anything else!
A neat tip on coil placement:
-
Try and issue an lf t55xx detect command. If the proxmark can detect the chip than you are close to a good spot (if
the chip is locked the proxmark will not return anything - this is part of what makes unlocking implants & antenna
placement tricky) -
After the lf t55xx detect, issue an lf t55xx trace a few times, if the proxmark returns the t55 tractability data screen
shown below you are in the “sweet spot” and writes should work cleanly. The reason for this is that it requires almost
perfect coupling to get clean reads from page1 of the t55 chip. -
On the above coil - the black mark seems to be the “sweet spot” even though it is on the back side.
There is much more to the antenna & coil side of things to be worked out. I am desperately seeking people to collaborate with on antenna design. The community needs better antennas to work with the proxmark3 and implants.
ISSUE #2 - THE WHITE CLONER AND “ID” MODE.
This thing is crazy just absolutely crazy, it very nearly drove me insane! After some hours of experimentation in HID mode, I found that the password set by this device is AA55BBBB but this seemed to only work on, and unlock chips written in HID mode, not in “ID” / EM410x mode. I was confused and frustrated as a few good friends had written to their implanted xEM with this device in that mode.
After some serious time spent sniffing and sorting data I realized that it was indeed the SAME password but there was something odd, I noticed one extra bit in the configuration data that was completely unknown to me at the time. After trolling through the datasheet linked above I thought that it was setting the chip in X-mode but that shouldn’t prevent writes.I noticed that the chip has a “test mode” bit that can be set, now this is not very well documented (publically at least) - there is one line in the entire datasheet that references it. Seems that once that bit is set, you need to write to the chip in test mode otherwise it will not respond. Luckily the proxmark3 has the “t” switch when writing - which writes in test mode.
This was a great relief - I managed to unlock someone’s chip for them.
There is one issue with this solution though. After using the testmode switch to write to Block 0 and unlock the tag. IF you choose to wipe the chip using the lf t55xx wipe command the command is able to wipe page1 of the chip - removing all traceability data / manufacturer information, this happens with some other Chinese t55xx chips too, not just the xEM. The issue then, is that a lot of cloners will not work with the t55 chip and the proxkmark will behave strangely - inconsistent reads etc…
What needs to be done to fix this is to restore the page1 data or create it. I’m unsure why having a blank page1 causes issues but to fix the problem you can simply restore the page1 data from another xEM implant.
Below is an example of the xEM page1 data. You can simply restore the two blocks and your xEM will respond happily.
proxmark3> lf t5 trace
T55x7 Trace Information
ACL Allocation class (ISO/IEC 15963-1) : 0xE0 (224)
MFC Manufacturer ID (ISO/IEC 7816-6) : 0x15 (21) - ATMEL France
CID : 0x01 (1) - ATA5577M1
ICR IC Revision : 2
Manufactured
Year/Quarter : 2014/2
Lot ID : 727
Wafer number : 16
Die Number : 8968
Raw Data - Page 1
Block 1 : 0xE0150A48 11100000000101010000101001001000
Block 2 : 0x2D782308 00101101011110000010001100001000
To restore the above tractability block data to block 0 of page 1 page one the commands are:
lf t55xx write b 1 d E0150A48 1
lf t55xx write b 2 d 2D782308 1
Making sure to have the 1 at the end of the command to reference page1.
Keep in mind that you are essentially spoofing the chips traceability data - I have not done enough digging to decipher what bits refer to what data but theoretically you could change the above data to whatever you want. As long it is within the standards specifications.
In summary:
Some of the blue cloners work very well, most don’t. Avoid if at all possible. If you do get one, it’s worth making a custom coil to avoid bad writes. This is something I am currently looking at, along with creating a better cloner. Generally, a rule of thumb with these is: if it reads bad i.e. hard to place / get a read - toss it, if it reads well and easily / consistently it may be kind of OK to use (at your own risk).
- The newer white cloners are just bad news - avoid even more so than the blue devices.
- We need better coils for the proxmark3 - can’t emphasize this enough.
- Test mode should be explored more - this is likely the way to un “bricking” some peoples xEM’s
- The xEM cloner project should be revived!
Based on the above information we can unlock our implants with the following commands and block data/
I have included the Block 0 configuration settings for all common modes with and without password protection:
EM4100 NO PWD-------------------00148041
EM4100 PWD ACTIVE-------------00148051
HID NO PWD-------------------------00107060
HID PWD ACTIVE-------------------00107071
BLANK t55 config--------------------00088040
Blue HID / EM Cloner:
lf t55xx write b 0 d ******** p 51243648
White multi-frequency HID mode:
lf t55xx write b 0 d ******** p AA55BBBB
White multi-frequency EM / ID mode:
lf t55xx write b 0 d ******** p AA55BBBB t
Note that where ******** you need to put the correct Analogue Block 0 settings for the specific mode that you currently have the xEM in. I have also included the necessary Block 0 settings if you want to keep your tag password protected.
So that is my take on the xEM and cloning issues - I hope it can help some of you out.
Happy holidays everyone! ![]()
~TH